How Qualys Drives PCI DSS 4.0 Compliance for File Integrity Monitoring
The Payment Card Industry Data Security Standard (PCI DSS) is a well-known rule for compliance by merchants and entities involved in payment card processing. The new PCI DSS 4.0 standard specifies a broad range of technical and process requirements to ensure the safety of payment cardholder data or sensitive authentication data or could impact the security of the cardholder data environment (CDE). Among these are a dozen sub-requirements for file integrity monitoring (FIM). This blog provides a review of PCI DSS 4.0 compliance requirements and how Qualys helps organizations to automatically comply with the FIM sub-requirements.
About PCI DSS 4.0 and Qualys
The six goals and twelve requirements of PCI DSS 4.0 cover a broad range, and many of these elements are things you would ordinarily do anyway for implementing and maintaining a comprehensive enterprise cybersecurity program. That is why the Qualys TruRisk Platform plays a key role as it helps drive an organization’s PCI DSS 4.0 compliance process in two important ways:
One of these is enabling automatic documentation of compliance – essentially, a status check of whether many of the controls for PCI DSS 4.0 requirements are in place, and whether they are doing their respective jobs. Second, with various integrated Qualys security applications such as VMDR, Patch Management, File Integrity Monitoring, and others, the platform also provides specific controls for a robust subset of PCI DSS 4.0 requirements. Implementation leverages several of the more than two dozen Qualys applications that are integrated within the Qualys TruRisk Platform.
This blog focuses on how Qualys helps with the subset of requirements for FIM.
Why File Integrity Monitoring Is Needed for PCI DSS 4.0
File integrity monitoring is essential for compliance with PCI DSS 4.0 as it helps identify unauthorized changes to critical files that could lead to loss or compromise of payment cardholder data or sensitive authentication data, security breaches, brand damage, and litigation. File changes may be the first or only indication that a firm has been breached in a cybersecurity attack or compromised through errors by either personnel or system updates. FIM serves a major role in protecting modern hybrid cloud environments, particularly after a breach has occurred and there is an urgent need to detect lateral movement, theft of sensitive data, or other damage.
The main idea of FIM is to reduce noise. The FIM solution is applied to files that undergo frequent changes, such as log files, configuration files, or temporary files, so it may generate many alerts, leading to noise or excessive notifications. This can make it difficult for administrators or security teams to distinguish between legitimate and potentially malicious changes.
Leading analysts report that a top challenge in many firms relates to false positive alerts. Some organizations have reported spending 25 percent of IT and analyst time to sort through indicators of compromise (IOCs) to find events of interest. Many firms also noted that other FIM solutions can generate many false alerts that require IT tickets and analyst triage to investigate. High noise can be a severe problem for firms regulated by PCI DSS 4.0. Ponemon Institute studies show that most organizations ignore over 30 percent of false positive alerts, typically due to limited resources and time for investigation. Given the new, more stringent guidelines, auditors may flag this, which could trigger audit failures. More importantly, ignored alerts could lead to security breaches. Qualys File Integrity Monitoring (FIM) offers advanced noise cancellation that dramatically reduces false positive alerts to eliminate these risks.
How Qualys Helps You Comply With FIM Requirements in PCI DSS 4.0
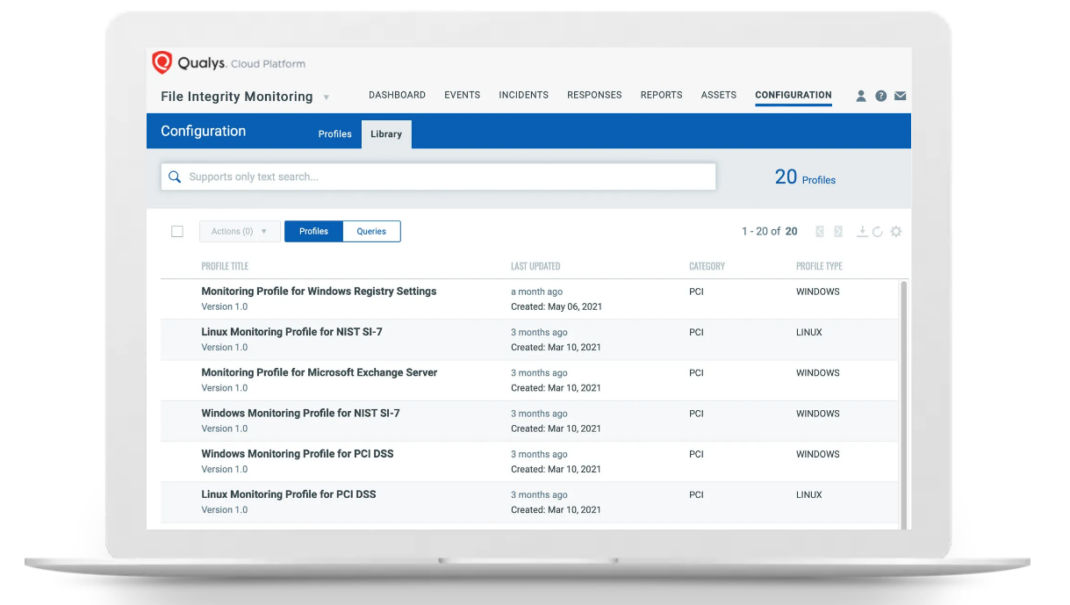
Qualys File Integrity Monitoring (FIM) provides a finely tuned library of critical file paths to be monitored to reduce noise. By leveraging this library, administrators can benefit from preconfigured monitoring settings that are tailored to specific industries, compliance requirements, or best practices. These libraries typically include critical system files, configuration files, application files, directories and registry objects that are most vulnerable to unauthorized changes or tampering.
Using this finely tuned library of critical file paths helps streamline the setup process and reduces the need for manual configuration, as Qualys FIM already includes common file paths that are likely to be monitored in most environments. It also helps minimize noise by focusing monitoring efforts on the most important files and directories.
Qualys FIM focuses on about a dozen requirements in PCI DSS 4.0 related directly to monitoring vulnerable files. These include several in Requirement 10: Log and monitor all access to system components and cardholder data, and Requirement 11: Test security of systems and networks regularly. For a comprehensive analysis of all PCI DSS 4.0 requirements using FIM, please check this link for a detailed matrix.
Learn More
To learn more details about PCI DSS, read the full text of PCI DSS 4.0 and other supporting documents in the PCI DSS v4.0 Resource Hub on the PCI Council website.
For full details on how Qualys enables PCI DSS 4.0 compliance, download our whitepaper, “PCI DSS 4.0: How Qualys Puts You in the Driver’s Seat for Compliance.”
- See our blog, Is Your FIM Solution Cost and Time Efficient?
- Qualys FIM Datasheet (download PDF)
- Essential FIM Must-Haves for Security and Compliance Practitioners (download PDF)
We also invite you to learn more about how you can use Qualys to achieve PCI DSS 4.0 compliance and start your free trial.
Contributors
- Eran Livne, Qualys Product Management
- Dave Buerger, Qualys Product Marketing