Understanding CVSS v4 and everything you need to know
On November 1st, 2023, the Common Vulnerability Scoring System version 4 (CVSS v4) was officially launched in General Availability (GA) following a period of public preview and feedback collection. This launch was orchestrated by the Forum of Incident Response and Security Teams (FIRST), marking a significant update to the CVSS standard that was last revised over eight years ago with the release of CVSS v3.0 in June 2015. The objective behind this latest iteration, CVSS v4, is to offer enhanced fidelity in vulnerability assessment for the industry and the public.
This new version incorporates various refinements, including a more granular breakdown of the Base Metrics to offer a nuanced understanding and assessment of vulnerabilities. Additionally, CVSS v4 introduced new nomenclature to denote combinations of Base, Threat, and Environmental metrics alongside new Base metric values for User Interaction, which are categorized as either Passive or Active. For an in-depth look at these changes, refer to our detailed blog post.
The success of CVSS v4 hinges on widespread adoption by the cybersecurity vendors and community, clarity and ease of use of its refined metrics, and precise vulnerability evaluations. Integration with existing systems, vendor support, and active community and regulatory engagement are critical. Its real-world effectiveness, coupled with a feedback loop for continuous improvement and timely updates in response to emerging threats, will determine its long-term impact and utility in enhancing cybersecurity measures.
Upon the official release of CVSS v4, it is anticipated that the National Vulnerability Database (NVD) may commence issuing updates and additional CVSS v4 data in the later part of the first half of 2024. This timeframe is also when we foresee a broader uptake of CVSS v4 beginning to take shape.
CVSS 4 vs. 3.1 What Has Changed in the Latest Version
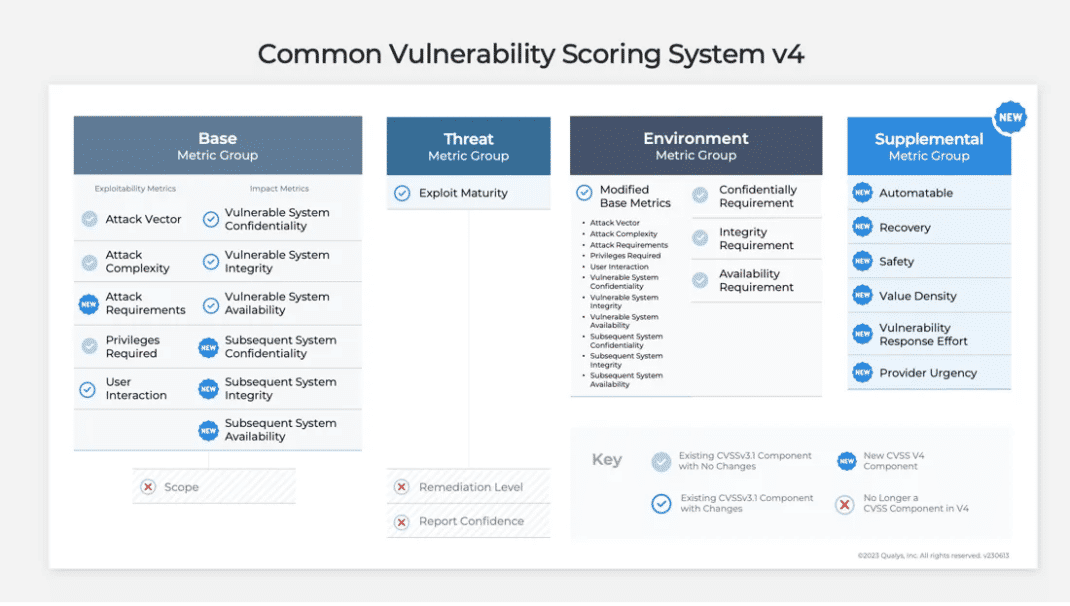
The figure below provides an overview of the changes between CVSS v3.1 vs CVSS v4.0.
What Is New In CVSS v4.0?
Nomenclature
The CVSS framework always consisted of three metric groups, i.e. Base, Temporal, and Environment. However, due to the popularity of the CVSS Base Score, it became synonymous with the overall CVSS score. CVSS score is not just a base case. To stress the importance of this, the following new nomenclature was adopted by CVSS v4:
| CVSS Nomenclature | CVSS Metrics Used |
|---|---|
| CVSS-B | Base metrics |
| CVSS-BE | Base and Environmental metrics |
| CVSS-BT | Base and Threat metrics |
| CVSS-BTE | Base, Threat, Environmental metrics |
Supplemental Metric Group
CVSS v4.0 introduces a new optional metric group called the “Supplemental Metric Group.” It provides metrics that describe and measure additional extrinsic attributes of a vulnerability. The Supplemental Metric Group aims to provide contextual information that consumers can use to take additional actions that help them in further risk analysis. It is important to note that Supplemental metrics are optional, and they do not have any impact on the calculated CVSS scores. Supplemental metrics to help you better understand extrinsic questions about vulnerabilities include:
| Safety | Does exploiting this vulnerability have a safety impact on an organization? |
| Automatable | Are attackers able to automate exploitation of this vulnerability? |
| Recovery | After an attack are the systems/component able to self-recover? |
| Provide Urgency | What is the rating provided by the vendor for this vulnerability? |
| Value Density | What resources will the attacker gain control over with a single exploitation event? |
Understanding the New Attack Requirement Metric and Its Role in Vulnerability Assessment
The new Attack Requirement (AT) metric aims to provide more granularity than provided by the “Attack Complexity (AC)” metric. This new metric captures the prerequisite deployment and execution conditions or variables of the vulnerable system that enable the attack.
Attack Complexity – Reflect the exploit engineering complexity required to evade or circumvent defensive or security-enhancing technologies. (Defensive measures)
Attack Requirements – Reflect the prerequisite conditions of the vulnerable component that make the attack possible.
What was updated/removed in CVSS v4.0?
Rename and Simplified Threat Metrics:
CVSS v4.0 renamed the “Temporal” Metric from CVSS v3.1 to “Threat Metrics.” CVSS v4.0 also retired the “Remediation Level (RL)” and “Report Confidence (RC)” metrics. In addition, the “Exploit Code Maturity (E)” was renamed to “Exploit Maturity (E).” The “High (H)” and “Functional (F)” values for this metric in CVSS v3.1 were also merged into one value of “Attacked (A)” in CVSS v4.0.
Update Base Metric: User Interaction (UI):
This metric captures the requirement for a user, other than the attacker, to participate in the successful compromise of the vulnerable component. CVSS v4.0 proposes the User Interaction (UI) metric to be more granular. CVSS v3.1 the User Interaction (UI) metric had values None(N) or Required(R). With CVSS v4.0 this metric now provides more granularity to the amount of interaction required as Passive (P) or Active (A). See more details at: https://www.first.org/cvss/v4.0/specification-document
Scope (S) Metric Removed in CVSS Version 4 Update
One of the CVSS v3.1 Base Metric of Scope(S) was retired in CVSS v4.0 due to the lack of clarity on the usage of this metric. This led to inconsistent scoring among vulnerabilities by different product providers. Due to this reason, the Scope Metric was retired in favor of two sets of impact metrics:
- Vulnerable System Impact – Confidentiality (VC), Integrity (VI), Availability (VA)
- Subsequent System(s) Impact – Confidentiality (SC), Integrity (SI), Availability (SA)
Other Updates and Changes in CVSS Version 4
Apart from these changes, CVSS v4.0 provides improved guidance to CVSS analysts to produce consistent scores, guidance on scoring vulnerabilities in software libraries etc. CVSS v4.0 is designed to support multiple CVSS scores for the same vulnerability that affects multiple products, platforms, operating systems, etc. It also provides guidance to extend the CVSS framework for other industry sectors such as privacy, automotive, etc.
TruRisk vs CVSS 4.0 A Smarter Approach to Risk Scoring
CVSS 4.0 represents a decent upgrade compared to CVSS 3.1, primarily due to the renaming of key metrics such as Temporal to Threat Metrics. This change makes it much easier for end users to evaluate the severity of a vulnerability. The inclusion of fine-grained details regarding user interaction required for vulnerability exploitation is also a welcome addition.
However, alongside the beneficial changes in version 4.0, there is also an increase in complexity. One longstanding issue with CVSS ratings has been the potential for inconsistencies in how individuals/vendors rate vulnerabilities. Moreover, with the introduction of more variables, the resulting scores can vary.
Ultimately, when assessing the risk of a vulnerability, the key metric that truly matters is the exploitability (which CVSS 4.0 addresses), evidence of exploitation (which it does not), and the likelihood of exploitation (as referenced by EPSS).
An ideal score is one that takes into account the CVSS rating to evaluate the technical severity and combines it with the exploitability factors referenced above. This is where TruRisk scores come into play, as it assists organizations in assessing the true risk of a vulnerability by considering multiple factors. These scores are designed to be easily understandable, even for non-technical teams, and greatly simplify the implementation of risk-based vulnerability management. See what goes into Qualys TruRisk scores here.
CVSS 4.0: FAQs on the Latest Version
When can we expect to see CVSS v4 scores in Qualys VMDR?
CVSS v4 scoring will be integrated into Qualys VMDR while vendors begin to include CVSS v4 scores in their security advisories.
How soon will vendors start incorporating CVSS v4 scores in their advisories?
The timeline for vendors to include CVSS scores in their advisories is outside our direct knowledge. However, this may begin by Q1 2024, following the estimated adoption trends.
Will the introduction of CVSS v4 affect my TruRisk scores?
The rollout of CVSS v4 is not expected to impact TruRisk scores directly. These scores should remain consistent pre- and post-introduction of CVSS v4.0.
Conclusion
CVSS v4.0 provides consumers with fine, granular metrics to better understand the technical characteristics of vulnerabilities. With the simplification of Temporal Metrics along with the addition of granular Base and Environmental Metrics, it aims to help consumers better understand the risk of vulnerabilities. With the addition of Supplemental Metrics, CVSS v4.0 consumers will be able to better communicate extrinsic characteristics of vulnerabilities, which will help customers better assess their risk and drive effective remediation.
Hi Saeed,
This is a great article; I read it when it was first published!
However, I noticed that Qualys is reporting it with a CVSS v3.1 score of 8.4.
Given the fundamental differences between CVSS v4.0 and v3.1, including updated metrics and scoring logic, I’m curious how this translation was performed. Specifically, does Qualys recalculate the score based on v3.1 metrics, or is there a mapping logic being applied? Also, is there a way to retrieve the exact v3.1 vector string used?
By the way, I really enjoy tuning into your monthly Patch Tuesday webinars. It is insightful!
Regards,
Yomi