Apache Tomcat HTTP Request Smuggling Vulnerability (CVE-2021-33037)
A vulnerability (CVE-2021-33037) discovered this year in Apache Tomcat causes incorrect parsing of the HTTP transfer-encoding request header in some circumstances, leading to the possibility of HTTP Request Smuggling (HRS) when used with a reverse proxy. HTTP Request Smuggling (HRS) is a web application vulnerability that enables an attacker to craft a single request that hides a second request within the body of the first request.
Qualys Web Application Scanning has added a new QID that detects this vulnerability by sending a request to the target server to determine if it is exploitable. Once detected, the vulnerability can be remediated by upgrading to Apache Tomcat 10.0.7, 9.0.48, 8.5.68 versions or to the latest version of Apache Tomcat. Qualys highly recommends upgrading all affected instances of Tomcat.
About CVE-2021-33037
Apache Tomcat is an open source web server and servlet container developed by the Apache Software Foundation.
According to CVE-2021-33037, Apache tomcat versions 10.0.0-M1 to 10.0.6, 9.0.0.M1 to 9.0.46 and 8.5.0 to 8.5.66 are vulnerable to this vulnerability.
This vulnerability occurs because vulnerable versions of Apache tomcat do not correctly parse the HTTP transfer-encoding request header in some circumstances. Not parsing the request header based on the specification leads to the possibility to request smuggling. The potential for the vulnerability is a high possibility when the server is configured with a reverse proxy. Specifically – Tomcat incorrectly ignored the transfer encoding header if the client declared it would only accept an HTTP/1.0 response; Tomcat honored the identify encoding; but did not ensure that, if present, the chunked encoding was the final encoding.
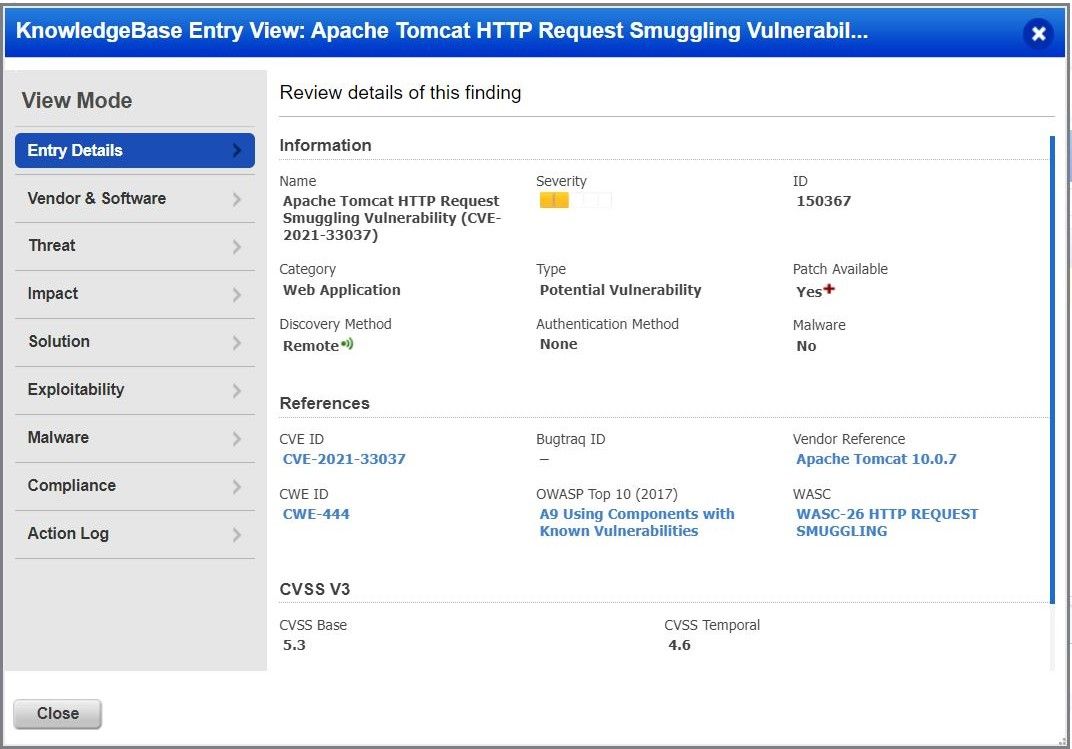
Detecting vulnerability with Qualys WAS
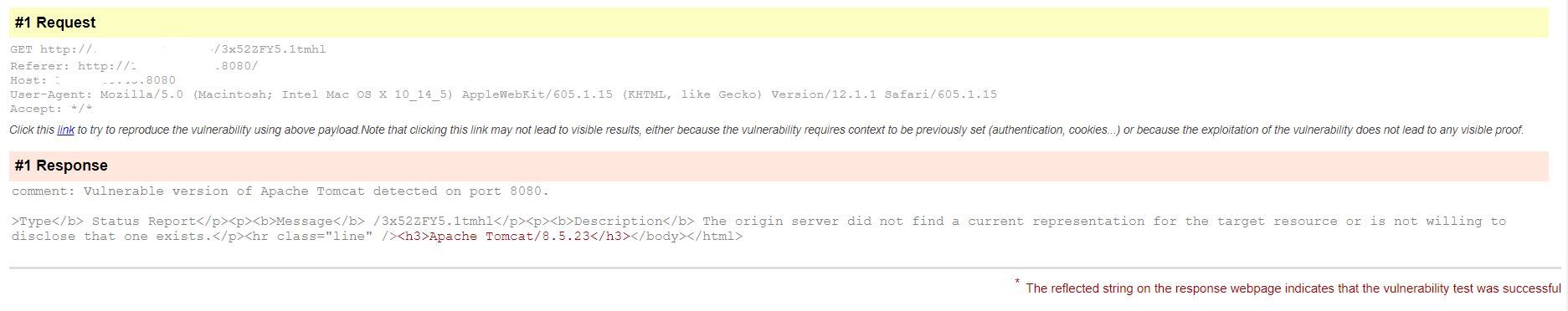
Customers can detect this vulnerability with Qualys Web Application Scanning using QID 150367. This vulnerability is detected based on the installed version. We make a request to GET /QUALYSTESTRANDOM.1tmhl HTTP/1.0. This request helps in retrieving the installed version of Apache Tomcat in the banner of the response.
Report
Once the vulnerability is successfully detected by Qualys WAS, users shall see similar kind of results in the vulnerability scan report:
Solution
The vulnerability has been discovered in the current year but it’s been prevalent and observed frequently.
Hence, we highly recommend to upgrade to the Apache Tomcat 10.0.7, 9.0.48 , 8.5.68 versions or to the latest version of Apache Tomcat.
Vendor Reference
https://tomcat.apache.org/security-10.html#Fixed_in_Apache_Tomcat_10.0.7
CVE Details
https://nvd.nist.gov/vuln/detail/CVE-2021-33037
Contributor
Sheela Sarva, Director, Quality Engineering, Web Application Security, Qualys
hi Raval, if you consider the architecture with tomcat which is placed behind F5 loadbalancer, will this version change fix the vulnerability or is there any other method to fix this vulnerability ?
Hello Murat, In addition to version change on tomcat side, you might also want to look at advisory from F5 – https://support.f5.com/csp/article/K32469285